Technology Category
- Cybersecurity & Privacy - Cloud Security
- Infrastructure as a Service (IaaS) - Cloud Computing
Applicable Industries
- Life Sciences
- National Security & Defense
Applicable Functions
- Quality Assurance
Use Cases
- Regulatory Compliance Monitoring
- Tamper Detection
Services
- Cloud Planning, Design & Implementation Services
About The Customer
Courtagen Life Sciences, Inc. is a leading provider of innovative genomic and proteomic products and services for physicians and the diagnostics industry. Founded in 2012, the company is dedicated to helping clinicians make better decisions regarding patient care. Courtagen is relentlessly focused on applying next-generation sequencing technology to help patients and doctors drive personalized, precision medicine. To concentrate on this key mission, Courtagen outsources its network and communications infrastructure, with Amazon Web Services playing an integral role in supporting the firm’s operations.
The Challenge
Courtagen Life Sciences, a leader in genomic services, relies heavily on Amazon Web Services (AWS) for its network and communications infrastructure. This cloud-based solution offers agility, cost savings, scalability, and support for users worldwide. However, to be successful, the solution must also provide comprehensive security and support regulatory compliance. Courtagen required a security solution that would work smoothly with its cloud environment and provide comprehensive protection against network attacks and data breaches, agility and flexibility to support changing needs, and simple management. The solution also needed to comply with HIPAA and other security regulations and requirements, seamlessly integrate with AWS, support secure access by mobile employees, and be scalable to support additional users.
The Solution
Courtagen adopted the Check Point Virtual Appliance for Amazon Web Services to extend robust security to the cloud. This virtual appliance is a security gateway for virtual environments in the Amazon Cloud, allowing Courtagen to prevent network attacks and data breaches, while enabling secure connectivity to Amazon’s cloud computing environment. The solution provides robust security to support Courtagen's cloud-based IT, support for dispersed and mobile employees and partners, and reliable operation for critical business operations. The Check Point solution allows Courtagen to quickly enable advanced security for assets in the Amazon Cloud, apply a Check Point Virtual Appliance with one click in Amazon Cloud, and manage security in the Cloud with industry-leading security administration. It also supports a single security policy for cloud and on-premise assets from one console, simplifies compliance and audits with unified logs and reporting, and supports a variety of Check Point Software Blades for security in the Amazon Cloud.
Operational Impact

Case Study missing?
Start adding your own!
Register with your work email and create a new case study profile for your business.
Related Case Studies.

Case Study
Data Capture for Afghanistan Forces
Electronic equipments on the field of Afghanistan provided information on the status of the vehicle and to identify potential threats surrounding it to the British Force. The monitoring and interpretation of this data requires robust and sophisticated digitization for data capture and communication.
Case Study
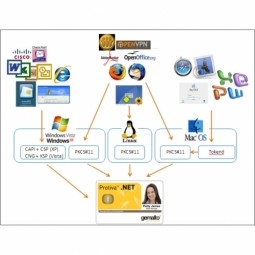
Corporate Identity Solution Adds Convenience to Beckman Coulter
Beckman Coulter wanted to implement a single factor solution for physical and remote logical access to corporate network. Bechman Coulter's users were carrying smart card badges for doors, but also needed a one-time password token to access to our corporate network when they were not in the office. They wanted to simplify the process.
Case Study
Enhancing Security and Compliance in Remitly's Global Money Transfer Service with Fastly
Remitly, an online remittance service, was faced with the challenge of securing its proprietary global transfer network. The company needed a security solution that could meet PCI requirements and protect customers' sensitive transactions through its mobile application. The solution had to be capable of defending against new and emerging attack types without impacting performance. Remitly also had to deal with irregular traffic patterns, such as a sudden spike in account transfers from a small network segment on the Pacific coastline of South America. The company needed to determine in real time whether such traffic indicated an attack or valid requests. A traditional web application firewall (WAF) would not be able to distinguish this traffic, potentially leading to customer frustration if the IP was blacklisted.

Case Study
Embracing Business Success in Real Time
· Increase control over growing Big Data to improve business decisions · Manage data for 28,000 biotechnology stockkeeping units in the fields of microbiology, molecular biology, animal cell cultures, plant tissue cultures, and lab ware for laboratory chemicals · Accelerate report generation and analysis with real-time data

Case Study
Major Aerospace Company Automates Asset Management
The O&M division of an aerospace and global security company was using spreadsheets to manually track more than 3,000 assets assigned to students and staff. Maintaining audit trails for this high volume of equipment became increasingly time-consuming and challenging. The chore involved knowing precisely what equipment was on hand, what had been issued, its location and the name of the custodial owner of each item. Every aspect of this task was carried owner of each item. Every aspect of this task was carried out by individuals with spreadsheets. Manually documenting the full lifecycle of each asset added to the burden. This included tracking maintenance requirements and records, incidents and damages, repairs, calibrations, depreciation, and end-of-life data.

Case Study
Securing a Large Data Center in the EMEA Region: An IoT Case Study
A leading data-center operator in the EMEA region, with multiple facilities spanning over 25,000 square meters, faced significant security challenges. The operator experienced interruptions in their internal IT network due to unsupervised work of third-party technicians. Despite having a high-end building control system that provided 24x7 monitoring and control to all the building’s infrastructure, the data center was vulnerable from a cyber perspective as it was connected to the IT network infrastructure. The operator launched an urgent OT cyber security project that included both IT-OT network segmentation and OT network asset mapping and anomaly detection. The main objectives were to harden the security of the server systems, secure the facility’s power supply and server cooling system, strengthen the segmentation between building and operational systems, create a visual OT network map, and set up a system for presenting supply-chain attacks that may threaten the data center through equipment vendors’ maintenance activities.







