技术
- 分析与建模 - 机器学习
- 分析与建模 - 预测分析
适用行业
- 生命科学
- 国家安全与国防
适用功能
- 采购
- 质量保证
用例
- 库存管理
- 篡改检测
服务
- 云规划/设计/实施服务
- 测试与认证
关于客户
AODocs 为各行业的客户提供服务,重点关注技术。他们目前正在扩展到医疗保健和金融服务等受到严格监管的行业。
挑战
即使实时工具正在将协作提升到一个新的水平,许多公司仍然依赖拼凑在一起的本地系统进行文档管理。
解决方案
AODocs 提供了一个与 Google Workspace 集成的内容服务平台,使企业能够有效地组织数据和文档。它提供权限和所有权控制、自动化工作流程、保留策略以及对标准和法规的遵守。
运营影响
数量效益

Case Study missing?
Start adding your own!
Register with your work email and create a new case study profile for your business.
相关案例.

Case Study
Data Capture for Afghanistan Forces
Electronic equipments on the field of Afghanistan provided information on the status of the vehicle and to identify potential threats surrounding it to the British Force. The monitoring and interpretation of this data requires robust and sophisticated digitization for data capture and communication.
Case Study
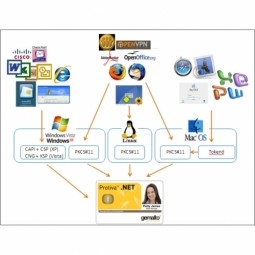
Corporate Identity Solution Adds Convenience to Beckman Coulter
Beckman Coulter wanted to implement a single factor solution for physical and remote logical access to corporate network. Bechman Coulter's users were carrying smart card badges for doors, but also needed a one-time password token to access to our corporate network when they were not in the office. They wanted to simplify the process.
Case Study
Enhancing Security and Compliance in Remitly's Global Money Transfer Service with Fastly
Remitly, an online remittance service, was faced with the challenge of securing its proprietary global transfer network. The company needed a security solution that could meet PCI requirements and protect customers' sensitive transactions through its mobile application. The solution had to be capable of defending against new and emerging attack types without impacting performance. Remitly also had to deal with irregular traffic patterns, such as a sudden spike in account transfers from a small network segment on the Pacific coastline of South America. The company needed to determine in real time whether such traffic indicated an attack or valid requests. A traditional web application firewall (WAF) would not be able to distinguish this traffic, potentially leading to customer frustration if the IP was blacklisted.

Case Study
Embracing Business Success in Real Time
· Increase control over growing Big Data to improve business decisions · Manage data for 28,000 biotechnology stockkeeping units in the fields of microbiology, molecular biology, animal cell cultures, plant tissue cultures, and lab ware for laboratory chemicals · Accelerate report generation and analysis with real-time data

Case Study
Major Aerospace Company Automates Asset Management
The O&M division of an aerospace and global security company was using spreadsheets to manually track more than 3,000 assets assigned to students and staff. Maintaining audit trails for this high volume of equipment became increasingly time-consuming and challenging. The chore involved knowing precisely what equipment was on hand, what had been issued, its location and the name of the custodial owner of each item. Every aspect of this task was carried owner of each item. Every aspect of this task was carried out by individuals with spreadsheets. Manually documenting the full lifecycle of each asset added to the burden. This included tracking maintenance requirements and records, incidents and damages, repairs, calibrations, depreciation, and end-of-life data.

Case Study
Securing a Large Data Center in the EMEA Region: An IoT Case Study
A leading data-center operator in the EMEA region, with multiple facilities spanning over 25,000 square meters, faced significant security challenges. The operator experienced interruptions in their internal IT network due to unsupervised work of third-party technicians. Despite having a high-end building control system that provided 24x7 monitoring and control to all the building’s infrastructure, the data center was vulnerable from a cyber perspective as it was connected to the IT network infrastructure. The operator launched an urgent OT cyber security project that included both IT-OT network segmentation and OT network asset mapping and anomaly detection. The main objectives were to harden the security of the server systems, secure the facility’s power supply and server cooling system, strengthen the segmentation between building and operational systems, create a visual OT network map, and set up a system for presenting supply-chain attacks that may threaten the data center through equipment vendors’ maintenance activities.







